| vuln.sg Vulnerability Research Advisory |
by Tan Chew Keong  Summary
Summary
A vulnerability has been found in QuarkXPress. When exploited, the vulnerability allows execution of arbitrary code when the user imports text from a MSWord 6 document (DOC) file.  Tested Versions
Tested Versions
 Details
Details
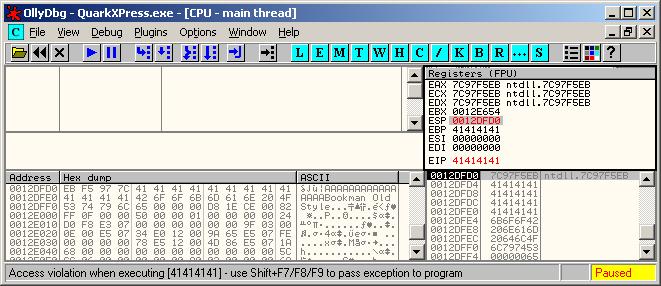
A stack-based buffer overflow vulnerability exists within the MSWord text-import extension ("Word 6-2000 Filter.xnt") that is distributed with QuarkXpress 7.2. The purpose of this extension is to allow the user to import text into the layout from a MSWord DOC file using the "Rectangle Text Box" tool. The boundary error occurs when the "Word 6-2000 Filter.xnt" DLL is handling the font-names that were read from a MSWord 6 document (DOC). The vulnerable function uses the "lstrcpy()" function to perform unsafe copying of each font-name that is read from the DOC file into a 256-byte stack buffer. The unsafe "lstrcpy()" occurs at ImageBase + 0x0000F608 in "Word 6-2000 Filter.xnt". This can be exploited to trigger a stack-based buffer overflow via a specially crafted DOC file that contains an overly long font-name. In order to exploit this vulnerability successfully, the user must be convinced to import text from a malicious MSWord DOC file. Execution of arbitrary code using this vulnerability has been confirmed on English WinXP SP2. The following screen capture shows that it is possible to overwrite the saved EIP when importing text from a MSWord 6 DOC file that contains an overly long font-name.
 POC / Test Code
POC / Test Code
The following POC DOC files will exploit the vulnerability to run calc.exe or crash QuarkXPress 7.2. The code execution POC has been successfully tested on English WinXP SP2.
Instructions to reproduce the vulnerability:
 Patch / Workaround
Patch / Workaround
Do not import text from non-trusted MSWord document (DOC) files.  Disclosure Timeline
Disclosure Timeline
2007-06-23 - Vulnerability discovered. |
| Contact |
| For further enquries, comments, suggestions or bug reports, simply email them to |