| vuln.sg Vulnerability Research Advisory |
by Tan Chew Keong  Summary
Summary
A vulnerability has been found in E-Post Mail Server. When exploited, the vulnerability allows an anonymous attacker to obtain the POP3 password of any known user from the POP3 service without requiring any logon.  Tested Versions
Tested Versions
The vendor also issues a patch for E-Post Mail Server Enterprise Version 4.10.  Details
Details
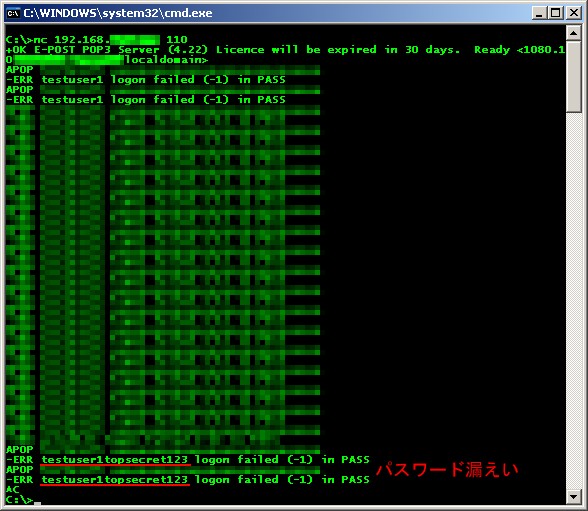
This advisory discloses a vulnerability in the POP3 service of the E-Post Email Server. When exploited, the vulnerability allows an anonymous attacker to obtain the POP3 password of any known user from the POP3 service without requiring any logon. Successful exploit requires that the attacker knows the POP3 account name (email address) of the victim. By issuing several specially-crafted APOP commands to the POP3 server, the user's password will be displayed back to the attacker in the POP3 error message. The vulnerability is due to a coding error in the APOP processing code in EPSTPOP3S.EXE 4.22, and is not related in any way to the MD5 collision weakness in APOP authentication. Full details of the vulnerability was sent to the vendor, but omitted from this advisory. For example, in the screenshot below, the password of testuser1 is revealed as topsecret123.
 POC / Test Code
POC / Test Code
Details of how to reproduce the issue was sent to vendor.  Patch / Workaround
Patch / Workaround
The vulnerability was fixed in EPSTPOP3S.EXE version 4.23. Vendor's advisory in Japanese.  Disclosure Timeline
Disclosure Timeline
2008-04-17 - Vulnerability Discovered. |
| Contact |
| For further enquries, comments, suggestions or bug reports, simply email them to |