| vuln.sg Vulnerability Research Advisory |
by Tan Chew Keong  Summary
Summary
A vulnerability has been found in PowerArchiver. When exploited, the vulnerability allows execution of arbitrary code when the user opens a malicious ISO file.  Tested Versions
Tested Versions
PowerArchiver version 9.64.02 (English) with PAISO.DLL 1.7.3.0 (1.7.3 beta)  Details
Details
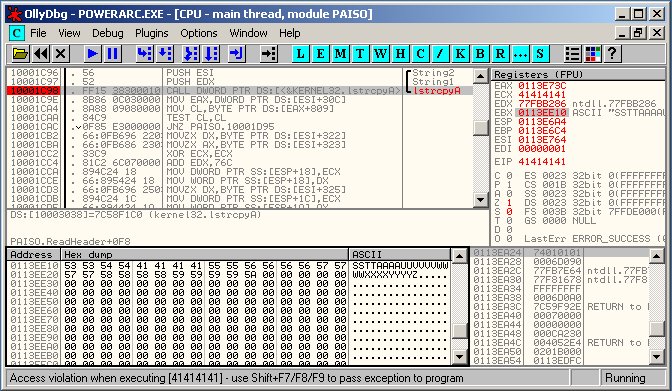
This advisory discloses a buffer overflow vulnerability in PowerArchiver. The stack-based buffer overflow occurs when PowerArchiver is constructing the full pathname of a file within an ISO image. This can be exploited to cause a stack-based buffer overflow and allows execution of arbitrary code. In order to exploit this vulnerability successfully, the user must be convinced to open a malicious ISO image file. The buffer overflow occurs within the LoadTree() and ReadHeader() functions of PAISO.DLL (version 1.7.3.0) that is distributed with PowerArchiver. The LoadTree() and ReadHeader() functions contruct the full pathname of each file in the ISO image by reading the directory entries within the ISO file. The directory name that is read from each directory entry is concatenated together using lstrcatA(), and finally with the filename. Subsequently, the constructed full pathname is copied into a fixed-length stack buffer using the unsafe lstrcpyA() function. The length of each directory name is limited by the ISO format. However, it is possible create an ISO image that contains a file nested within several level of directories. This will create a full pathname that overflows the stack buffer, thus allowing the saved EIP and SEH handler to be overwritten.
 POC / Test Code
POC / Test Code
The following POC ISO file will exploit the vulnerability to run calc.exe or crash PowerArchiver. The code execution POC has been successfully tested on English WinXP SP2 and Win2K SP4.
Instructions:
 Patch / Workaround
Patch / Workaround
Update to version 9.64.03.  Disclosure Timeline
Disclosure Timeline
2006-12-17 - Vulnerability Discovered. |
| Contact |
| For further enquries, comments, suggestions or bug reports, simply email them to |