| vuln.sg Vulnerability Research Advisory |
by Tan Chew Keong  Summary
Summary
A vulnerability has been found within the archive extraction functionality of net2ftp. When exploited, this vulnerability allows an anonymous attacker to retrieve and potentially delete files from the web server where net2ftp is hosted. Execution of arbitrary PHP code is also possible if the web server directory is writable.  Tested Versions
Tested Versions
 Details
Details
This advisory discloses a vulnerability within the archive extraction functionality of net2ftp. When exploited, this vulnerability allows an anonymous attacker to retrieve and potentially delete files from the web server where net2ftp is hosted. Execution of arbitrary PHP code is also possible if the web server directory is writable. The net2ftp web-based FTP client allows the user to connect to an FTP server and to extract a TAR/ZIP file on the FTP server in a few simple steps. It does this in the following way.
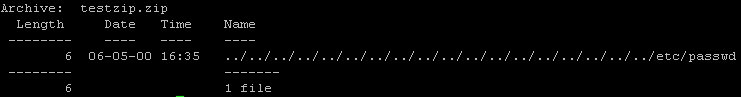
A malicious user can create a specially-crafted TAR/ZIP archive that contains files with directory traversal sequences in their filenames. When such an archive is extracted by net2ftp, it can cause net2ftp to upload arbitrary files from the web server to the FTP server, with privileges for the web server process. In addition, the files will be extracted outside of the temp directory. By creating a specially-craft TAR/ZIP archive that causes PHP files to be extracted into the web server directory (via directory traversal sequences in their filenames), arbitrary code execution on the web server is possible. An example of such an archive is shown below.
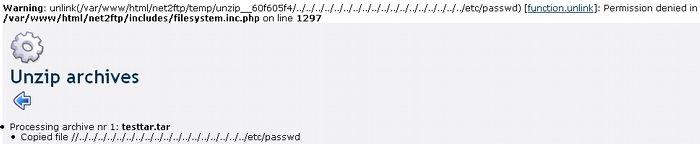
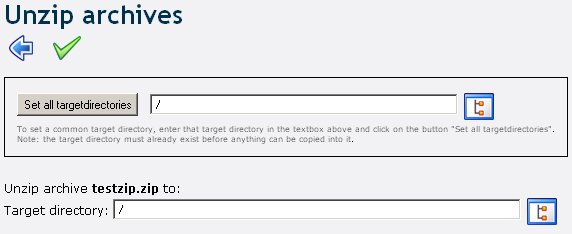
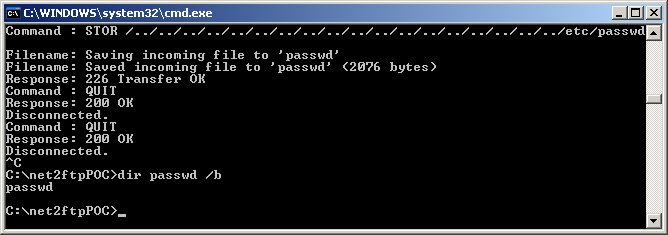
Extracting such an archive with net2ftp will cause net2ftp to upload "/documentroot/net2ftp_root/temp/unzip__xxxxxxxxx/../../../../../../../../../../../../../../../../../../etc/passwd" to the FTP server. This allows an attacker to steal /etc/passwd or any other files that are accessible to the web server process. For example, by stealing "settings.inc.php", an attacker will be able to find out the net2ftp admin username and password. Note that if net2ftp is hosted on a Windows-based web server, the backslash directory traveral sequence ..\ can also be used. In addition, after the file is uploaded to the FTP server, net2ftp will attempt to delete that file. This means that if the web server process has write access to that file, it will be deleted. To allow execution of arbitrary PHP code, the attacker must be able to access the extracted PHP file before net2ftp completes its upload to the FTP server and deletes the file. This can be archived by creating a specially-craft FTP server that sleeps for 10 seconds before completing the STOR request from net2ftp. This delay should give the attacker sufficient time to access the extracted PHP file before it is deleted. This vulnerability can be exploited from two places in net2ftp.
The screenshot below shows net2ftp attempted to delete /etc/passwd after uploading it to the FTP server.
 POC / Test Code
POC / Test Code
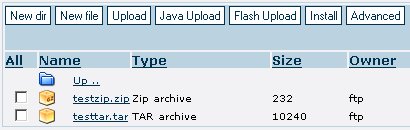
Please download the POC here and follow the instructions below. Preparations for testing:
Instructions for testing FTP client:
 Patch / Workaround
Patch / Workaround
Update to version 0.97 (stable), that was released on June 9, 2008.  Disclosure Timeline
Disclosure Timeline
2008-06-05 - Vulnerability Discovered. |
| Contact |
| For further enquries, comments, suggestions or bug reports, simply email them to |