| vuln.sg Vulnerability Research Advisory |
by Tan Chew Keong  Summary
Summary
A vulnerability has been found in IBM Lotus Notes. When exploited, the vulnerability allows execution of arbitrary code when the user views a malicious AMI Pro file.  Tested Versions
Tested Versions
 Details
Details
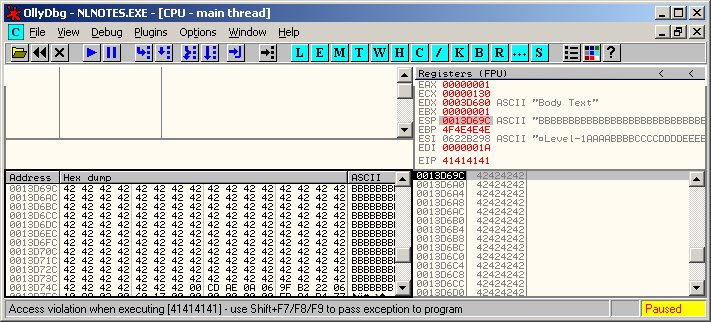
The buffer overflow occurs within lasr.dll when parsing an AMI Pro document (.sam) file. In several places within the DLL, the unsafe "lstrcpy()" function is used to copy each line read from the file into fixed sized stack and heap buffers. There are no length checks before performing the string copy operation. Hence, it is possible to create an AMI Pro file that contains overly long lines that will trigger the buffer overflow when viewed within Lotus Ntoes. In order to exploit this vulnerability successfully, the user must be convinced to view a malicious AMI Pro document file attachment using the built-in viewer in Lotus Notes. The Ollydbg screen capture below shows that the vulnerability can be used to overwrite the saved EIP.
 POC / Test Code
POC / Test Code
The following POC AMI Pro document (SAM) file will exploit the vulnerability in IBM Lotus Notes to execute the harmless calculator (calc.exe). The POC has been successfully tested on English Windows XP SP2 with Lotus Notes version 7.0.2.
Instructions:
 Patch / Workaround
Patch / Workaround
Update to version 7.0.3. See vendor's technote for more information.  Disclosure Timeline
Disclosure Timeline
2007-01-07 - Vulnerability Discovered. |
| Contact |
| For further enquries, comments, suggestions or bug reports, simply email them to |