| vuln.sg Vulnerability Research Advisory |
by Tan Chew Keong  Summary
Summary
A vulnerability has been found in FireFTP add-on for Firefox. When exploited, this vulnerability allows an anonymous attacker to write files to arbitrary locations on a Windows user's system.  Tested Versions
Tested Versions
The vulnerability is also confirmed in development version 0.98.20080405  Details
Details
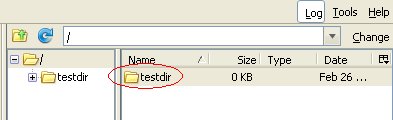
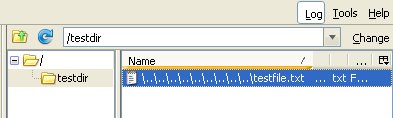
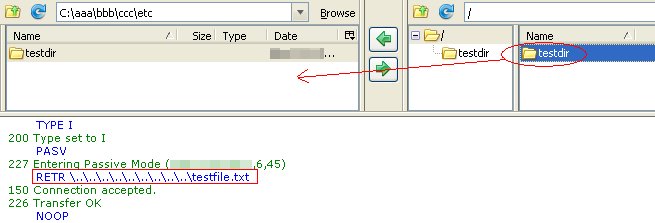
This advisory discloses a vulnerability in the FireFTP add-on for Firefox. When exploited, this vulnerability allows an anonymous attacker to write files to arbitrary locations on a Windows user's system. The FTP client does not properly sanitise filenames containing directory traversal sequences (backslash) that are received from an FTP server in response to the MLSD and LIST commands. Examples of such responses from a malicious FTP server is shown below. Response to MLSD: type=file;modify=20080227074710;size=20; \..\..\..\..\..\..\..\..\..\testfile.txt\r\n Response to LIST: -rw-r--r-- 1 502 502 4096 Mar 01 05:37 \..\..\..\..\..\..\..\..\..\testfile.txt\r\n By tricking a user to download a directory from a malicious FTP server that contains files with backslash directory traversal sequences in their filenames, it is possible for the attacker to write files to arbitrary locations on a user's system with privileges of that user. An attacker can potentially leverage this issue to write files into a user's Startup folder and execute arbitrary code when the user logs on.  POC / Test Code
POC / Test Code
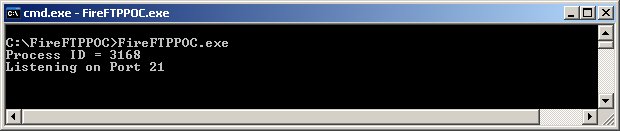
Please download the POC here and follow the instructions below. Instructions:
Hence, by tricking a user to download a directory from a malicious FTP server, an attacker can potentially leverage this issue to write files into a user's Startup folder and execute arbitrary code when the user logs on.  Patch / Workaround
Patch / Workaround
The vulnerability has been fixed in development version 0.98.20080518 and in release version 0.97.2. Code change in CVS.  Disclosure Timeline
Disclosure Timeline
2008-05-09 - Vulnerability Discovered. |
| Contact |
| For further enquries, comments, suggestions or bug reports, simply email them to |