| vuln.sg Vulnerability Research Advisory |
by Tan Chew Keong
 Summary
Summary
An archive extraction directory traversal vulnerability has been found in RbigSoft Easy Unrar, Unzip & Zip. When exploited, this vulnerability allows an anonymous attacker to write files to arbitrary locations within the SD card of the user's Android device.  Tested Versions
Tested Versions
 Details
Details
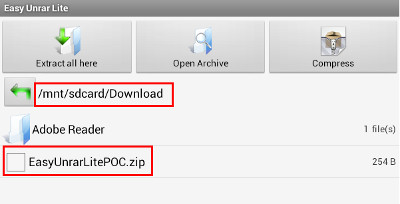
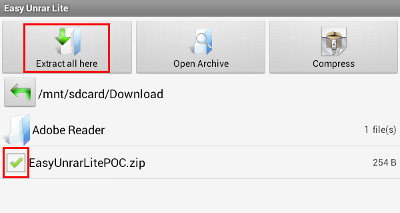
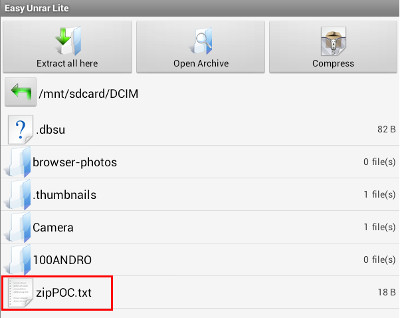
This advisory discloses an archive extaction directory traversal vulnerability in RbigSoft Easy Unrar, Unzip & Zip. When exploited, this vulnerability allows an anonymous attacker to write files to arbitrary locations within the SD card of the user's Android device. When extacting compressed files from an archive, the extraction functionality does not properly sanitise compressed files that have directory traversal sequences in their filenames. By tricking a user to extract a specially crafted archive containing files with directory traversal sequences in their filenames, an attacker can write files to arbitrary locations within the SD card of the user's Android device, possibly overwriting the user's existing files. For example, a malicious archive can contain a compressed file with the following filename: /../../../../../../../../mnt/sdcard/DCIM/zipPOC.txt  POC / Test Code
POC / Test Code
Please download the POC ZIP archive here and follow the instructions below. Note that other archive types are potentially also affected. Instructions for testing Directory Traversal in Archive Extraction:
Hence, by tricking a user to extract a specially-crafted archive, an attacker can potentially exploit this issue to write files into arbitrary locations within the SD card in the user's Android device, or to overwrite files in known locations within the SD card. For example, an attacker who is aware of the filenames of the user's photo in the /mnt/sdcard/DCIM/ directory can exploit this vulnerability to overwrite the user's photo files.  Patch / Workaround
Patch / Workaround
Avoid extacting untrusted archives.  Disclosure Timeline
Disclosure Timeline
2013-05-20 - Vulnerability Discovered. |
| Contact |
| For further enquries, comments, suggestions or bug reports, simply email them to |